Intro
2025 was a pivotal year for cybersecurity. With digital transformation accelerating across industries, remote work becoming the norm, and AI reshaping IT defense, the threat landscape grew more complex – and more interesting. From record-breaking breaches to groundbreaking innovations, this recap highlights the most important events and trends that defined cybersecurity in 2025.

Biggest Trends of 2025
AI and Machine Learning in Security
Cybersecurity teams increasingly leveraged AI to detect and respond to threats faster. Machine learning algorithms now identify anomalies in real-time, helping organizations stay ahead of sophisticated attacks.
Zero Trust Adoption
The “trust no one, verify everything” model continued to grow. Companies embraced zero trust architectures to minimize internal and external risk, replacing traditional perimeter-based security approaches.
Cloud Security Focus
As organizations migrated more workloads to the cloud, attackers targeted misconfigured cloud environments and APIs. Cloud-native security solutions and continuous monitoring became essential.
IoT and OT Threats
The proliferation of connected devices expanded attack surfaces. Critical infrastructure and operational technology (OT) systems faced growing risks from ransomware and state-sponsored attacks.
Ransomware Evolution
Ransomware attacks grew more sophisticated, with double-extortion tactics becoming common -encrypting data and threatening to leak it publicly if ransom demands weren’t met.
Regulatory Push
Global privacy regulations such as GDPR, CCPA, and emerging frameworks in Asia and Europe forced organizations to tighten data protection, leading to more secure IT practices across industries.

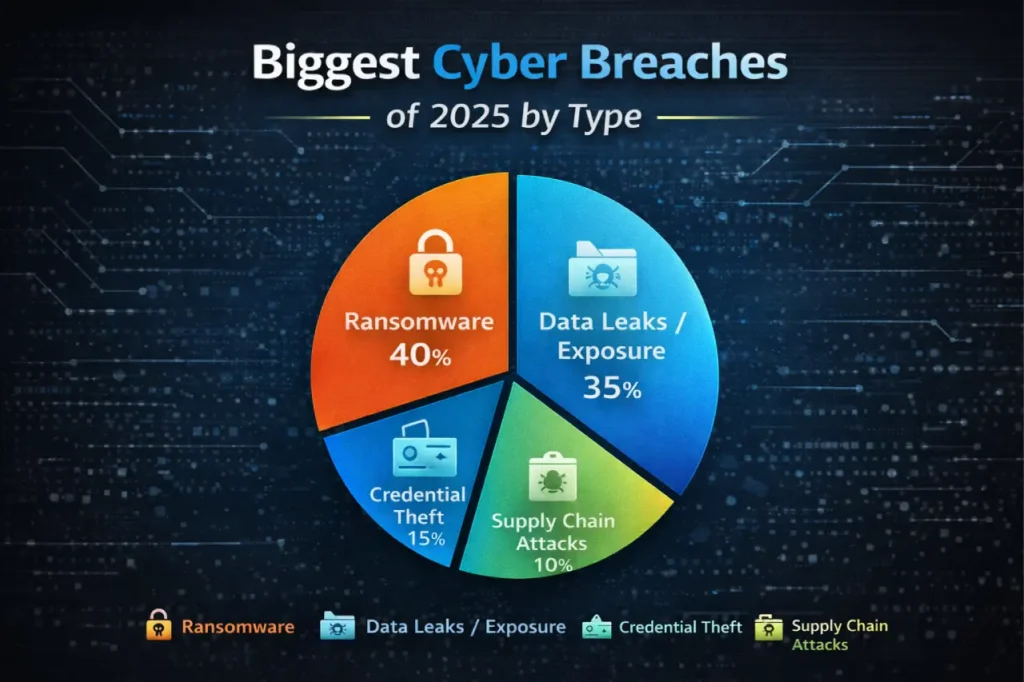
Biggest Breaches of 2025
In 2025, cyber incidents spanned sectors – from retail giants and insurance providers to healthcare and telecommunications. South Korea’s Coupang lost data on over 33 million users, while Aflac’s attack exposed over 22 million policyholders, underscoring persistent risks in consumer and financial services. Healthcare systems like Covenant Health were hit by widespread ransomware, and telecom infrastructure such as SK Telecom saw authentication data compromised, revealing new threat vectors for identity fraud. These breaches highlight that no industry – regardless of size or sector – is immune to modern cyber risks.
1.Coupang Data Breach (South Korea)
South Korean e‑commerce giant Coupang suffered a major breach affecting about 33.7 million users. Personal information including names, email addresses, and phone numbers was compromised, prompting a national reaction and compensation package for affected users. The Times of India+1
Industry statement:
“This breach underscored how even top-tier retailers with massive digital footprints remain vulnerable to sophisticated API and authentication attacks – signalling a need to elevate secure software development and third‑party risk management.”
2.Aflac Insurance Breach (US)
Insurance giant Aflac confirmed that a cyberattack exposed sensitive policyholder data for over 22 million customers. The HIPAA Journal
Industry statement:
“High‑value personal data remains a prime target; this breach highlights the need for stronger encryption, identity protection frameworks, and continuous monitoring across financial and insurance sectors.”
3.Covenant Health Ransomware Attack (Healthcare)
Nearly 478,000 patients were affected in a major ransomware incident at Covenant Health, showcasing how healthcare systems remain heavily targeted. Tom’s Guide
Industry statement:
“Healthcare providers continue to struggle with legacy systems and insufficient segmentation, making the sector a persistent target for ransomware actors.”
4.SK Telecom SIM Authentication Breach (Telecom)
South Korea’s largest carrier, SK Telecom, disclosed a breach involving stolen SIM authentication data for around 27+ million subscribers, compromising authentication mechanisms and risking SIM cloning exploits. Βικιπαίδεια
Industry statement:
“Telecom infrastructure – once considered robust — is now a frontline in identity attacks, urging deeper investment in secure authentication and hardware safeguards.”
5.Jaguar Land Rover (JLR) Data Leakage (Automotive / Supply Chain)
In March 2025, the automotive giant Jaguar Land Rover suffered a major breach by the HELLCAT ransomware group, leaking internal documents and source code due to compromised employee credentials. PKWARE®
Industry statement:
“Supply chain risks manifested once again, reinforcing how interconnected corporate ecosystems expand the attack surface when partners lack stringent cybersecurity controls.”
6.Qantas Third‑Party Customer Data Exposure (Aviation)
Hackers accessed up to 5.7 – 6 million customer records from a third‑party platform used by Qantas – including personal and loyalty data. FortifyData
Industry statement:
“Third‑party vendors are as critical to secure as the core business itself – a breach from an integration partner can impact millions and damage trust.”
Bonus: Wide‑Scale Credential Leak (Systemic Risk)
In 2025, researchers reported an aggregated database of about 16 billion stolen credentials drawn from various leaks, highlighting widespread credential hygiene issues across enterprises and consumer services. Secureframe
Industry statement:
“Credential reuse remains one of the largest systemic vulnerabilities; even strong perimeter defenses are bypassed when identity hygiene isn’t enforced at scale.”
MegaBank Ransomware Attack: A sophisticated attack exposed 50 million customer records, highlighting weaknesses in banking cybersecurity.
Popular Software Supply Chain Breach: A widely used software library was compromised, impacting thousands of businesses worldwide.
Healthcare Data Leaks: Multiple hospitals faced data leaks, exposing sensitive patient information and emphasizing the need for stronger healthcare cybersecurity protocols.
**Lesson Learned: No organization is immune. Proactive monitoring, employee training, and robust incident response are no longer optional – they’re critical.
Biggest Innovations in Cybersecurity
Cybersecurity innovation in 2025 focused on automation, AI, and proactive defense:
-
AI-driven Security Operations Centers (SOC): Automation helped analysts detect threats faster and reduce response time.
-
Next-Gen Endpoint Protection: Solutions combining AI with behavioral analytics prevented ransomware and malware at the device level.
-
Security Orchestration, Automation, and Response (SOAR): Automated workflows improved threat investigation and response efficiency.
-
Post-Quantum Cryptography Research: Organizations began preparing for the quantum era, exploring algorithms resistant to quantum attacks.
-
Open-Source Security Tools Gaining Traction: Platforms like Wazuh, Elastic Security, and others became central to both small teams and enterprise setups.
Lessons for 2026
As we move into 2026, organizations should focus on:
-
Strengthening Cloud Security: Continuous monitoring and misconfiguration prevention are key.
-
AI-Powered Security: Leverage AI for real-time threat detection and incident response.
-
Employee Awareness: Human error remains a top risk – training and phishing simulations are essential.
-
Compliance Readiness: Keep up with global privacy regulations and security frameworks.
-
Investing in Open-Source Tools: Flexible and community-supported tools help small teams achieve enterprise-level monitoring.
Conclusion
2025 reinforced a clear reality: cybersecurity is no longer optional. From record-breaking breaches to revolutionary tools, the year taught us that proactive defense, continuous learning, and embracing innovation are critical to staying safe.
***Want to stay ahead in 2026? Start integrating AI-driven monitoring, zero trust principles, and cloud security best practices today.